
Yutaka Niibe gniibe@identi.ca
Maebashi, Japan
GNU wannabee ['gnu:be], FSIJ chairman, Debian Developer
Financially stable (GnuPG)
2021-12-14T01:33:25Z via Pumpa To: Public CC: Followers
The project is now funded well. Thank you all supporters and users.
https://www.gnupg.org/donate/index.htmlAlexandre Oliva likes this.
 My point is that "used to" was added in the page.
My point is that "used to" was added in the page.
https://dev.gnupg.org/rD0775ff5ec916ce8efa68281d5b8e85ddd3098016Free (as in freedom) smart card reader firmware implementation
2021-11-05T04:48:13Z via Pumpa To: Public CC: Followers
GnuPG 2.3.1 is released
2021-04-21T00:23:02Z via Pumpa To: Public CC: Followers
Bug fixing (mostly for build) release. It's a worth try.Scorpio shared this.
Libgcrypt 1.9.3 is released
2021-04-19T23:46:45Z via Pumpa To: Public CC: Followers
It would be good if this was the 1.9.0. I mean, there are more fixes for regressions (than we had expected).
Good things are the build process has been improved.Ploting X448
2021-04-12T02:08:16Z via Pumpa To: Public CC: Followers
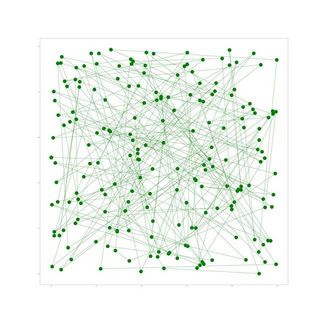 Green plots are the first 200 points of X448.
Green plots are the first 200 points of X448.
Green star is the generator.GnuPG 2.3.0 released
2021-04-07T23:54:08Z via Pumpa To: Public CC: Followers
It comes with Ed448/X448 support.Sway
2021-04-06T05:45:29Z via Pumpa To: Public CC: Followers
I start using Sway to test Wayland on this machine.
It seems that input method support is not that mature in the protocol.
Thus, I fixed my implementation (of Emacs Lisp) for Japanese input.Ed448 for Gnuk
2021-03-17T23:50:52Z via Pumpa To: Public CC: Followers
Running 100 iterations, signing on FST-01 (Cortex-M3 @ 72MHz), it's like:
real 0m15.929s
user 0m0.973s
sys 0m0.262s
Yes, generated signature is good:
~$ gpg --verify /tmp/a1.asc /etc/motd
gpg: NOTE: THIS IS A DEVELOPMENT VERSION!
gpg: It is only intended for test purposes and should NOT be
gpg: used in a production environment or with production keys!
gpg: Signature made Thu Mar 18 08:47:45 2021 JST
gpg: using EDDSA key 91B78334699E9155A9E0651CBE352A1DCF455BFF
gpg: Good signature from "Kunisada Chu " [ultimate]X448 for Gnuk
2021-03-09T05:41:52Z via Pumpa To: Public CC: Followers
Running 100 iterations, decrypting on FST-01G (Cortex-M3 @ 72MHz), it's like:
gpg: encrypted with cv448 key, ID F6FA616F8E4378B9, created 2021-03-09 "Kunisada Chu <chuji@gniibe.org>" real 0m34.189s user 0m2.512s sys 0m0.387s gniibe@iwagami:~/work/gnuk/gnuk/src$That is, 0.34189 second for a single decryption process.
It's good enough for me.
Gnuk 1.2.17
2021-02-26T05:17:30Z via Pumpa To: Public CC: Followers
Mainly for GNU/Linux emulation, new Gnuk is out.
https://lists.gnupg.org/pipermail/gnuk-users/2021-February/000293.htmlsub and subs instruction (pre-UAL syntax, UAL syntax)
2021-02-25T03:12:26Z via Pumpa To: Public CC: Followers
I didn't know well about two different syntax in ARM assembler.
For UAL syntax (newer, which is usually used), it requires an explicit "s" suffix to specify flags being set, while pre-UAL syntax (older, which is used for Cortex-M0) assumes that implicitly.
In GCC, we have -masm-syntax-unified option.libgcrypt 1.9.2 released
2021-02-17T23:39:28Z via Pumpa To: Public CC: Followers
Well, 1.9.0 had point-zero release problem (= no one tests well until its release).
Now, it has support of Ed448/X448 curves.
Enjoy,Alexandre Oliva, nukem likes this.
GD32VF103 and its possible use for Gnuk
2020-09-30T23:59:47Z via Pumpa To: Public CC: Followers
GD32VF103, which comes with RISC-V core, is cheap and fast.
I ported Chopstx to GD32VF103, and am considering if it's good to port Gnuk.
Last month, when I found riscv-openocd merged the support of GD32VF103, I tried to use the debugger interface.
And... for my version (which I bought from Seeed), the Longan Nano, I can access its flash ROM content.
If my analysys is correct, it's a kind of matter for CVE, I suppose.
With help of my Chinese friends, I try to contact the vendor.
Happy Chinese Holiday Season!Alexandre Oliva likes this.
 And then, I was informed for this having many CVEs:
And then, I was informed for this having many CVEs:
https://github.com/JohannesObermaier/f103-analysis/
Well, mine is independent, and more easier to be attacked.Yutaka Niibe at 2020-10-02T01:46:05Z
geekable likes this.
Supporting Ed448 (GnuPG)
2020-06-24T01:21:24Z via Pumpa To: Public CC: Followers
I pushed the change to support Ed448 to GnuPG master:
https://dev.gnupg.org/rGa763bb2580b0d586a80b8ccd3654f41e49604f4fEd448 in libgcrypt
2020-06-10T23:59:57Z via Pumpa To: Public CC: Followers
X448 feature has been pushed to GnuPG master.
Now, I'm adding the support of Ed448 to libgcrypt so that it will be also supported by GnuPG.Supporting X448 (GnuPG)
2020-06-10T23:58:44Z via Pumpa To: Public CC: Followers
I pushed the change to support X448 to GnuPG master.
UI (displaying the name of algo, selecting it from tty or command line) needs some more changes, though.Bouncing GnuPG Logo
2019-12-26T23:33:30Z via Identi.ca Web To: Public CC: Followers
 It's running on the Longan-Nano board with RISC-V MCU named GD32VF103 (Bumblebee core).
It's running on the Longan-Nano board with RISC-V MCU named GD32VF103 (Bumblebee core).
I took a video, but I don't know how we can share a video with free software friendly way.
So, it's an image only for now.salyavin likes this.

Just for the record, you can upload videos here, to Pump.io, with a client capable of it, like Dianara.
And there's always a Mediagoblin or Nextcloud instance 😃
JanKusanagi at 2019-12-27T13:01:08Z
salyavin likes this.
"FSIJ" logo on 160x80 screen by RISC-V MCU
2019-12-01T23:49:16Z via Identi.ca Web To: Public CC: Followers
 Longan Nano comes with LCD display, which is connected through SPI.
Longan Nano comes with LCD display, which is connected through SPI.
I wrote a SPI driver for Chopstx.
This is an example.salyavin likes this.
2019-11-26T00:23:14Z via Identi.ca Web To: Public CC: Followers
Last week, I renewed IEEE membership, and got a sticker saying "KEEP CALM I'M IEEE MEMBER".
Then, yesterday, I received FSF Bulletin. #fsfbulletin
It was sent on November 11th, the one of binary days. :-)McClane likes this.