
Susan Pinochet sdp0@identi.ca
Atlanta, United States
avid computer user, former programmer, lover of good design, armchair philosopher, lesbian homemaker

jasonriedy@fmrl.me at 2015-11-20T20:23:41Z
Am I the only person who puts his finger too close to the scroll bar on android and becomes horribly annoyed?Susan Pinochet likes this.

You are definitely not alone. Wifh Andstatus would allow setting what side the scroll bar is on
Freemor at 2015-11-20T20:52:03Z
lnxwalt@microca.st likes this.

Avadiax at 2015-11-21T00:21:41Z
ISIL's professionally done TIME-like magazines explain why their way is the right way ... http://www.cracked.com/blog/isis-wants-us-to-invade-7-facts-revealed-by-their-magazine/Susan Pinochet likes this.

flow
The spring ran dry 4 months ago, and finally started flowing this week. The cistern is full, hurrah! Was down to ~1 month water.
Susan Pinochet, Charles Stanhope, Greg Grossmeier likes this.

Avadiax at 2015-11-17T16:14:29Z
Folks, that is why the battle against ISIL is going to be long and painful for everyone. http://www.telegraph.co.uk/news/worldnews/europe/france/12000928/The-worlds-determination-to-defeat-Isil-is-a-myth.htmlSusan Pinochet likes this.

Elena ``of Valhalla'' at 2015-11-17T12:35:13Z

Decoding Daesh: Why is the new name for ISIS so hard to understand? | Free Word CentreArabic translator Alice Guthrie explains how Daesh, the new name for ISIS, undermines the terrorist group, and asks why anglophone media can't understand it.
sazius at fmrl.me, Susan Pinochet, Claes Wallin (韋嘉誠) likes this.
Adam Moore (LÆMEUR), Claes Wallin (韋嘉誠), Claes Wallin (韋嘉誠) shared this.
 Best comment:
Best comment:
"""
I wonder why you avoided the better slang term (in the US) for jerks that try to impose their will on others: Douchebag or just douche. Sounds a lot like the arabic daish and is anything but complementary. Thanks for the excellent article.
"""
Can't figure out how to pronounce "Daesh"? Just call them Douche.Claes Wallin (韋嘉誠) at 2015-11-17T15:15:32Z
lnxwalt@microca.st, sazius at fmrl.me, Elena ``of Valhalla'' likes this.

The British Driving Rule
Elena ``of Valhalla'' at 2015-11-15T11:10:03Z
The British Driving RuleThe left side of the road is the right side of the road, and the right side of the road is the wrong side of the road.
Susan Pinochet, Kyosuke likes this.

GPL Enforcement and the Trans-Pacific Partnership
Software Freedom Conservancy at 2015-11-10T18:35:46Z
URL: https://sfconservancy.org/blog/2015/nov/09/gpl-tpp/
A Blog post by Bradley M. Kuhn and Karen M. Sandler
GPL Enforcement and the Trans-Pacific Partnership
Many people have criticized the proposed Trans-Pacific Partnership (TPP) treaty since the text was released. In particular, some of the terms in the agreement are bad for software freedom and other social justice causes. Despite the TPP's stated intention to bring "social benefits" in addition to economic growth, the terms of TPP work against social benefits and awards too much power and control to large multinational corporations, including proprietary software companies.
The agreement text is lengthy and complex, filed with bad provisions. A few days ago, the Free Software community uncovered the following text from the TPP:
1. No Party shall require the transfer of, or access to, source code of software owned by a person of another Party, as a condition for the import, distribution, sale or use of such software, or of products containing such software, in its territory.
2. For the purposes of this Article, software subject to paragraph 1 is limited to mass-market software or products containing such software and does not include software used for critical infrastructure.
3. Nothing in this Article shall preclude:
(a) the inclusion or implementation of terms and conditions related to the provision of source code in commercially negotiated contracts; or
(b) a Party from requiring the modification of source code of software necessary for that software to comply with laws or regulations which are not inconsistent with this Agreement.
4. This Article shall not be construed to affect requirements that relate to patent applications or granted patents, including any orders made by a judicial authority in relation to patent disputes, subject to safeguards against unauthorised disclosure under the law or practice of a Party.
The revelation of this clause has confused our community, as it appears as if this provision, once adopted, might impact or restrict the international operation of copyleft licenses. Below we explain that, while everyone should reject and oppose this provision — and the rest of TPP — this provision has no dramatic impact on copyleft licensing.
First, as others have pointed out, Party is a defined term that refers specifically to government entities that sign the treaty. As such, the provision would only constrain the behavior of governments themselves. There are some obviously bad outcomes of this provision when those governmental entities interfere with public safety and ethical distribution of software, but we believe this provision will not interfere with international enforcement of copyleft.
Copyleft licenses use copyright as a mechanism to keep software free. The central GPL mechanism that copyright holders exercise to ensure software freedom is termination of permission to copy, modify and distribute the software (per GPLv2§4 and GPLv3§8). Under GPL's termination provisions, non-compliance results in an automatic termination of all copyright permissions. In practice, distributors can chose — either they can provide the source code or cease distribution. Once permissions terminate, any distribution of the GPL'd software infringes copyrights. Accordingly, in an enforcement action, there is no need to specifically compel a government to ask for disclosure of source code.
For example, imagine if a non-US entity ships a GPL-violating, Linux-based product into the USA, and after many friendly attempts to achieve compliance, the violating company refuses to comply. Conservancy can sue the company in US federal court, and seek injunction for distribution of the foreign product in the USA, since the product infringes copyright by violating the license. The detailed reasons for that infringement (i.e., failure to disclose source code) is somewhat irrelevant to the central issue; the Court can grant injunction (i.e., an order to prevent the company from distributing the infringing product) based simply on the violator's lost permissions under the existing copyright license. The Court could even order the cease of import of the infringing products.
In our view, the violator would be unaffected under the above TPP provision, since the Court did not specifically compel release of the source code, but rather simply ruled that the product generally infringed copyrights, and their distribution rights had fully terminated upon infringement. In other words, the fact that the violator lost copyright permissions and can seek to restore them via source code disclosure is not dispositive to the underlying infringement claim.
While TPP thus does not impact copyright holders' ability to enforce the GPL, there are nevertheless plenty of reasons to oppose TPP. Conservancy therefore joins the FSF, EFF, and other organizations in encouraging everyone to oppose TPP.
Help support Conservancy and its efforts to defend the GPL by becoming a Supporter today.
Posted by Bradley M. Kuhn and Karen M. Sandler on November 9, 2015. Please email any comments on this entry to info@sfconservancy.org.
Susan Pinochet, Sajith Sasidharan, João Patrício, Jure Repinc (JLP) and 5 others likes this.
Luis Ángel Fernández Fernández, João Patrício, Jure Repinc (JLP), AJ Jordan and 8 others shared this.

David Thompson at 2015-11-11T19:36:34Z
"We view “reproducible builds” as a technical means to an end: that of guaranteeing user autonomy and safety."Elena ``of Valhalla'', guile, Susan Pinochet, Olivier Mehani and 6 others likes this.
Olivier Mehani, Christine Lemmer-Webber shared this.

Claes Wallin (韋嘉誠) at 2015-11-13T11:24:27Z
gregkh gets it:
"""
Where do you think that "new developers" come from? Do they show up in our inbox, with full knowledge of kernel internals and OS theory yet they somehow just can't grasp how to submit a patch correctly? Yes, they sometimes rarely do. But for the majority of people who got into Linux, that is not the case at all.
"""
http://thread.gmane.org/gmane.linux.kernel/2039243/focus=2041419
/via Developer recruitment and outreach, linked from that KS collection.Drew Fustini, Susan Pinochet likes this.


joeyh interview
Debian Project at 2015-03-01T04:13:28Z
joeyh interviewed about his life after Debian, bye :'(
Claes Wallin (韋嘉誠), Jakukyo Friel, Susan Pinochet, Lars Wirzenius and 5 others likes this.
Claes Wallin (韋嘉誠), Lars Wirzenius shared this.
 "I want to build worthwhile things that might last."
"I want to build worthwhile things that might last."
+12765 to that.Lars Wirzenius at 2015-03-02T18:19:35Z
Claes Wallin (韋嘉誠) likes this.

 Somebody help calm it down.
Somebody help calm it down.Susan Pinochet, Douglas Perkins, ben, Efraim Flashner likes this.
 In the office, on a glass door is a sign that reads, "Keep Clear" ...
In the office, on a glass door is a sign that reads, "Keep Clear" ...Susan Pinochet likes this.
 In the office, on a glass door is a sign that reads, "Keep Clear" ...
In the office, on a glass door is a sign that reads, "Keep Clear" ...Susan Pinochet likes this.

consumer electronics
10 tiny torx screws and masking tape. That's what I hate about taking a laptop apart. The fan yesterday developed a slight burr, almost unnoticable until you do and then annoying without end.
Had to work on it for 2 solid hours. My smallest torx bit didn't quite fit; lived in fear of stripping the screws. Rehearsed everything on my same-model parts laptop, and still hated every minute of it. Eventually I disconnected the fan, for now. Its cable was held down by a spot of masking tape. That's new; they must have changed cable lengths and this was some engineer's quick fix.
And that's what I hate about taking a laptop apart, I see the shortcuts, the screws that bite into plastic, the ribbon cables with their latches surely rated for < 100 cycles, the bits of tape. Once I've had a laptop apart I can never look at it quite the same way again, as a hunk of consumer electronics that is going to work for a while, until entropy eats it and it doesn't. I know , and somehow, when it comes to consumer hardware, I don't want to.
Software is so different for me, I had no problem PEEKing and POKEing away at the fan controller's bits last night, although I have not managed to adapt http://github.com/blan4/lenovo-yoga-fan-control/ to work with this model so far, and only managed to get the fan stuck on high, rather than turned off.
I want a bunnie laptop. If it's designed to be taken apart, it wouldn't bother me.
Susan Pinochet, Tyng-Ruey Chuang, Olivier Mehani, jasonriedy@fmrl.me and 1 others likes this.

long comment tail
I've had several recent blog posts on the front page of Hacker news. Generally the Sunday after I write them.
Often they get 30k page views and not a single comment (on the blog or HN), which is understandable since my blog has been somewhat esoteric lately. (My poor mum, trying to make sense of monads)
But then there's comments on 8 year old blog posts. Like http://joeyh.name/blog/entry/dealing_with_dialup/#comment-fbe83263f7eb32a36a35ce24f4cd73ef
This is something that worries me about the pump network BTW, discoverability for old posts is not very good. Most posts don't seem to be getting into the Internet Archive; it visits my identi.ca page only a few times a year, and Evan's only a little more often. I'll bet that google doesn't much notice when pump posts are shared and popular unless a traditional website links to them, either. This is likely not good for both long tail effects and network growth effects.
Jakukyo Friel, Claes Wallin (韋嘉誠), Susan Pinochet, jasonriedy@fmrl.me and 3 others likes this.
Claes Wallin (韋嘉誠) shared this.

winter in the South
On the porch swing in the sun, in bare feet and a t-shirt. Almost like it's not January. In 2 days, it might well be snowing.
Susan Pinochet, Greg Grossmeier, cmhobbs likes this.

Christine Lemmer-Webber at 2015-01-22T17:05:14Z
The most clear sign of insanity available is that you're using M-x ansi-term in emacs because you're too lazy to open a real terminal. Looks like I'm insane, then.
Claes Wallin (韋嘉誠), Douglas Perkins, jasonriedy@fmrl.me, Susan Pinochet likes this.
Claes Wallin (韋嘉誠), Claes Wallin (韋嘉誠), X11R5 shared this.

Location Sharing
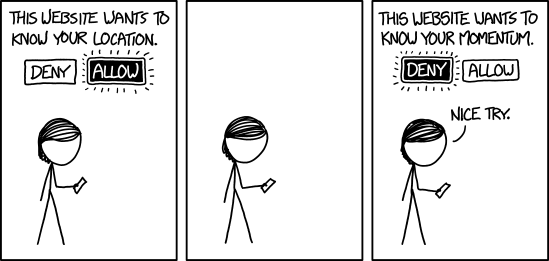
Our phones must have great angular momentum sensors because the compasses really suck.
http://xkcd.com/1473Vladimir, Susan Pinochet, Tsyesika@io.theperplexingpariah.co.uk, sazius likes this.
 I certainly laughed, but somebody here was saying "I don't get the joke" because the character is obviously not a subatomic particle. Tastes for humor can be very personal. :)
I certainly laughed, but somebody here was saying "I don't get the joke" because the character is obviously not a subatomic particle. Tastes for humor can be very personal. :)
Christine Lemmer-Webber at 2014-12-03T15:36:19Z
Are there many words worse than "webinar"?
Susan Pinochet, Stephen Michael Kellat, lnxwalt@microca.st, cmhobbs and 1 others likes this.
Stephen Michael Kellat, Claes Wallin (韋嘉誠) shared this.

Webisode is on the same league xD
JanKusanagi at 2014-12-03T15:37:15Z
Stephen Michael Kellat, Christine Lemmer-Webber likes this.

Bradley M. Kuhn at 2014-11-04T22:51:22Z
I'm seriously considering running for the state legislature wherever I move to next.
uıɐɾ ʞ ʇɐɯɐs, Susan Pinochet, Mike Linksvayer, Evan Prodromou and 3 others likes this.
Claes Wallin (韋嘉誠) shared this.