
Elena ``of Valhalla'' valhalla@identi.ca
2018-11-07T21:37:38Z via social.gl-como.it To: Public
learn.to/quote
The “properly quote eMail messages and on Usenet” documentation is hosted on a server that appears to not get too much care at the moment. I’ve dug out workable versions:...
www.mirbsd.org2018-11-02T17:09:58Z via social.gl-como.it To: Public

Update 26: Allwinner VPU driver accepted in upstream Linux! · Allwinner VPU support in the official Linux kernel
It's been a while since our last update, but there's now a major news to share: the Allwinner VPU Linux kernel driver is now in the upstream Linux kernel, it has been pulled by Linus Torvalds on October 30. Of course, together with the Allwinner VPU driver, the whole V4L2 request API patch series has been merged, which was a dependency of the Allwinner VPU driver. This all means that the next Linux kernel release (4.20 or 5.0, depending on how Linus decides to call it), will have the Allwinner VPU driver that was funded by this Kickstarter campaign!The main commit adding the Allwinner VPU driver is https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=50e761516f2b8c0cdeb31a8c6ca1b4ef98cd13f1.At the moment, the driver only supports MPEG2 decoding, but we have already submitted follow-up patch series adding H264 and H265 decoding. With the base driver merged, we expect that it should be a lot easier to get those additional improvements merged.In other news, Bootlin engineer Maxime Ripard gave a talk about this work at the Embedded Linux Conference Europe in Edinburgh, on October 22. The slides of the talk are available, as well as the video. Also as part of this conference, Maxime had a booth with a demo of the Allwinner VPU driver, see the poster of the booth.https://www.youtube.com/watch?v=KRrO9e5UugA
www.kickstarter.com @Gruppo Linux Como @LIFOLady Ada pendants and brooches
2018-10-29T21:31:58Z via social.gl-como.it To: Public
Part of my under-development #steampunk costume is a chatelaine, and I wanted to decorate the brooch with something adequate for an analytic engine programmer.
Today I finally managed to do some laser toner transfers on #cernit on a couple of brooches and pendants; the top right brooch is the one that will end up holding the chatelaine.
I've posted WIP pictures on pixelfed.
The image is the famous Ada Initiative design, but I've removed the frame for improved clarity in the small format and the edited SVG is on openclipart.clacke@libranet.de ❌ likes this.
2018-10-25T07:20:41Z via social.gl-como.it To: Public
♲ trashHeap@anticapitalist.party 2018-10-24 22:53:38:#FLOSS #phone people I know. We have a new project to obsessively follow. https://liliputing.com/2018/10/pine64-is-developing-a-linux-smartphone.html
And it seems it may not cost an arm and a leg...
#WillItRunDebian?
@Gruppo Linux Como2018-10-24T15:21:03Z via social.gl-como.it To: Public
♲ gl-como@social.gl-como.it 2018-10-24 09:53:53:Linux Day 2018 Varese-Como
La principale manifestazione italiana dedicata a Linux, al software libero, alla cultura aperta ed alla condivisione: decine di eventi in tutta Italia, centinaia di volontari coinvolti e migliaia di visitatori per celebrare insieme la libertà digitale!
Inizia:
Sabato 27 Ottobre 2018 @ 14:00
Finisce:
Sabato 27 Ottobre 2018 @ 19:00
Posizione:
MATTEO BECHINI likes this.
2018-10-23T18:40:31Z via social.gl-como.it To: Public
Petter Reinholdtsen: Web browser integration of VLC with Bittorrent support
Bittorrent is as far as I know, currently the most efficient way to distribute content on the Internet. It is used all by all sorts of content providers, from national TV stations like NRK, Linux distributors like Debian and Ubuntu, and of course the Internet archive. Almost a month ago a new package adding Bittorrent support to VLC became availabl...
people.skolelinux.org2018-10-18T15:59:51Z via social.gl-como.it To: Public
♲ lifo@social.gl-como.it 2018-10-18 15:58:05:Materiale Linux Day

Ieri mattina abbiamo ricevuto il materiale per il prossimo #LinuxDay.
Il LIFO collabora con @Gruppo Linux Como e LinuxVar all'organizzazione dell'edizione di Tradate, presso il FaberLab in via Europa
@glcomo2018-10-16T07:37:45Z via social.gl-como.it To: Public
♲ emanchado@diasp.org 2016-10-26 19:54:34:Really sad that people think "nerdy fantasy and dragons" when they think about role-playing games. Case in point: through the brilliant Jason Morningstar I just learned about a fascinating new RPG about dying languages. It's called Dialect and it's on Kickstarter right now.
From what I understand it's about inventing the story of a small, isolated community that has their own language/dialect, invent words for that language and see the community change over time, the language evolve, and, finally, the language die. Of course, this can be placed in any setting (a jungle, another planet, ...).
The linguist in me is super-excited. I think I'll buy it, even if I may never get the chance to play. I'm sure reading the book is going to be worth the price!
#linguistics #languages #kickstarter #rpg #roleplaying #games
Dialect: A Game about Language and How it Dies
Build a language, build a world. Who were the Isolation, and how were they lost? In this game, your language is the story.
www.kickstarter.com2018-10-13T18:27:59Z via social.gl-como.it To: Public
Tails - Our donation campaign for 2019 begins today
Every day, Tails helps thousands of people to safely use their computers online and offline. Tails is available for free because we believe that nobody should have to pay to be protected from surveillance and censorship. Tails is free software because if our source code was closed, there would be no way of verifying that it is secure. In today's In...
tails.boum.org2018-10-13T07:27:55Z via social.gl-como.it To: Public
♲ liberapay@framasphere.org 2018-10-12 16:44:33:Liberapay status update
No, we’re not dead.
Three months ago we announced that Liberapay was in trouble. Since then we’ve been working on adapting the platform to work with other payment service providers, and today we’re finally ready to announce that #Liberapay now supports two separate payment processors: Stripe and PayPal.What you need to do
If you use Liberapay to receive #donations: you need to connect at least one Stripe or PayPal account, otherwise donations to you cannot be processed. If both #Stripe and #PayPal are available in your country then we recommend setting up both.
If you’re a donor: you don’t have to do anything right now. You will automatically receive a notification when it’s time to renew your donations. Note: the page to manage your donations has been redesigned to fit how Liberapay works now, and also to fit small screens.
How Liberapay works now
As stated in our previous blog post the way donations are processed needed to evolve for Liberapay to be able to survive and grow. This announcement caused some confusion and worry, so here’s an attempt to better explain the change.
In the past when a user wanted to donate they were asked to add money into their “wallet”, and once the money had arrived it was transferred little by little every Wednesday to the donation recipient(s). This created a very long delay (sometimes years) between when the donor sent the money and when the beneficiary actually received all of it. During that time the money stayed idle in Mangopay wallets, not being useful to anyone.
Now the entire amount of a payment goes immediately to the Stripe or PayPal account of the recipient, there are no more wallets. However, the donations are still recurrent: the amount of money sent still corresponds to a specific number of weeks and the donor is still notified when it’s time to renew the #donation.
Let’s take an example: Alice wants to donate $1 per week to Bob, and she decides to send $12 for her first payment. In the old system the money would have gone into her Mangopay wallet, then every Wednesday $1 would have been transferred from that wallet to Bob’s wallet, until there wasn’t any money left in Alice’s wallet. In the new system the $12 go directly to the Stripe or PayPal account of Bob, and every week Liberapay subtracts $1 from the amount that Alice has paid in advance, until that number reaches zero. In both systems Alice receives an email notification after 12 weeks reminding her that it’s time to pay again, and Bob receives an email every week informing him that his income” is $1, even though in the new system Bob actually receives the $12 on the first week instead of $1 payments every week.
If Alice decides to modify the amount of her donation, then the date of the next payment changes accordingly. For example, if immediately after paying she increases her donation to $2 per week, then the renewal will be 6 weeks later instead of 12. However, if Alice decides to stop the donation she will not automatically receive a refund of the money she has paid in advance, because this isn’t implemented yet. If you stop a donation and you would like a refund please contact us.
A big shortcoming of the new system is that every donation has to be paid separately, which can be quite annoying if you have many of them. We’re planning to tackle this problem in two different ways: by avoiding it whenever possible (Stripe and PayPal both have partial support for doing multiple payments at once), and by making it easier to manage the multiple payments when we can’t bundle them all together. The latter involves helping the donor to schedule the payments in an optimal way, then either executing them automatically (if desired and possible) or simply notifying the donor when it’s time.
Another important issue is that PayPal payments are currently not anonymous, the donor and the recipient can see each other’s email address. We may be able to fix that in the future, it depends on getting approval from PayPal.
Finally, a drawback of abandoning wallets is that Liberapay’s team system relied heavily on them. We’ve been able to make donations to teams work again, but only in a simplistic way: when a donor wants to send money to a team our software selects one of the team’s members to receive it, whereas ideally the payment should be split into multiple transfers so that every member receives its share. This shortcoming means that some members can receive more money than they should, although over time the disparity should tend to disappear as new payments are received by the other team members.Status of Mangopay
We disabled adding money to a wallet on July 19th, and stopped processing transfers between wallets on August 21st. However, withdrawing money to a bank account is still possible. As of today €23.6k and $2.6k remain stored in 640 wallets. You may want to check your wallet.
Thanks to the donors who followed the recommendation in our previous blog post, a total of €37k and $5.8k was donated in advance, thus greatly reducing the short term impact of the Mangopay crisis on the available income of creators. Unfortunately €16.8k and $8k were refunded to donors instead, either by choice or by inaction (on August 25th we refunded as much of what was left in the wallets of donors as possible). Hopefully at least some of that money was donated in other ways.About Stripe and PayPal
Stripe and PayPal are both #payment services that can be used without Liberapay, whereas Mangopay accounts cannot be accessed directly by their owners and aren’t shared between platforms. This big difference means that if you were to stop using Liberapay you would still be able to receive #payments through Stripe and PayPal in other ways.
Stripe is a payment service designed to help businesses collect payments from their customers easily and securely. On Liberapay it allows donors to pay by card directly from our website, whereas PayPal payments require redirecting the donor to PayPal’s website. Stripe also supports other payment methods in addition to cards, the one we’re currently working on is the SEPA Direct Debit, which as you may know we used to support through #Mangopay.
Stripe’s biggest flaw is that it only supports sending money to a relatively small number of countries (less than 30), so some of our users cannot use it. This is one of the reasons why we also support PayPal, which operates pretty much worldwide (more than 200 countries).
While it is sad that Stripe isn’t more global, at least they’re clear about which countries they support, whereas Mangopay wasn’t clear at all and even silently dropped support for countries they had users in! Liberapay will work much better outside of Europe now that we use Stripe and PayPal instead of Mangopay, and we will be able to support many more #currencies in the future.Conclusion
Liberapay is recovering, but it will take at least several more months before everything is fully operational again.
Original post on #Medium
#OpenSource #en #Crowdfunding #Micropayments #Commons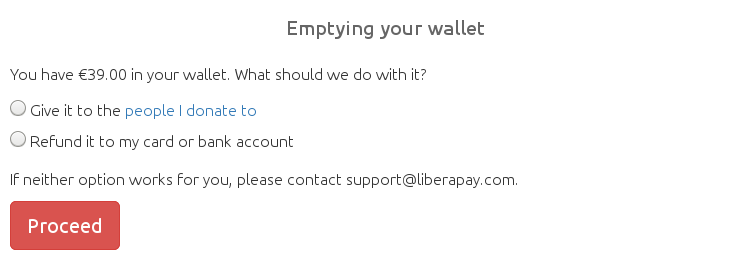
Liberapay is in trouble – Liberapay’s Blog – Medium
Our payment processor (Mangopay) is throwing us out. Liberapay won’t shut down, but the service will be disrupted until we can fully…
medium.comStephen Michael Kellat shared this.
2018-10-07T20:56:07Z via social.gl-como.it To: Public
♲ victorhck@pod.orkz.net 2018-10-07 12:30:05:Who is Jenny Everywhere? Modify and share this character


Heard of Jenny Everywhere? Me neither, until I was looking for media to use for an open source character drawing contest I was involved in. As I Googled my way around the internet, I happened upon Jenny Everywhere.
read more
Who is Jenny Everywhere? Modify and share this character
Heard of Jenny Everywhere? Me neither, until I was looking for media to use for an open source character drawing contest I was involved in. As I Googled my way around the internet, I happened upon Jenny Everywhere.
opensource.comastheroth likes this.
2018-09-27T16:28:54Z via social.gl-como.it To: Public

Censorship Project + A Brief History of Book Burning – Ex Urbe
Today I’m delighted to announce my big new project, a collaboration with Cory Doctorow and Adrian Johns: Censorship and Information Control during Information Revolutions You can learn about it from the project website, and support it on Kickstarter. The idea: Revolutions in information technology always trigger innovations in censorship and inf...
www.exurbe.com A (partially) crowdfunded project for a series of lectures and discussions on the history of censorship, involving Cory Doctorow, Adrian Johns, and Ada Palmer.
I've started to pledge at the the museum exhibit catalog level, and maybe I'll add more.Tyng-Ruey Chuang likes this.
2018-09-14T19:31:11Z via social.gl-como.it To: Public

Real Products That Exist: Teacup And Saucer Holsters
These are the ~$90 - $100 leather teacup and saucer holsters made by Etsy seller LeatherHeds for Steampunk style costumes, or anybody who just really needs a teacup and saucer at the ready at all times. Because you never...
geekologie.com #steampunk #tea
I think I may eventually need one of those...2018-09-11T18:49:23Z via social.gl-como.it To: Public
mjg59 | The Commons Clause doesn't help the commons
mjg59 | The Commons Clause doesn't help the commons
mjg59.dreamwidth.org2018-09-11T18:46:47Z via social.gl-como.it To: Public
♲ valhalla@mastodon.social 2018-09-09 20:41:30:A marble white cat from Colonnata, near Carrara.
#cats #mastocats #catstodon #catsOfMastodon
2018-08-26T07:43:45Z via social.gl-como.it To: Public
♲ wired@pod.cyberdungeon.de 2018-08-25 11:20:02:Phone Numbers Were Never Meant as ID. Now We’re All At Risk
#all #meant #never #now #numbers #phone #risk #security #were
Phone Numbers Were Never Meant as ID. Now We’re All At Risk
Services increasingly rely on your phone number to know who you are—and that's increasingly a problem.
www.wired.comStephen Michael Kellat likes this.
Stephen Michael Kellat shared this.
2018-07-31T19:42:50Z via social.gl-como.it To: Public
♲ valhalla@mastodon.social 2018-07-30 20:21:00:#DebConf18 videos are being published on https://meetings-archive.debian.net/pub/debian-meetings/2018/DebConf18/
more than half of the recorded talks are already available, and more are being worked on right now.Index of /pub/debian-meetings/2018/DebConf18
meetings-archive.debian.net2018-07-27T07:35:55Z via social.gl-como.it To: Public
feed discovery and live bookmarks should not be removed from firefox
tl;dr: Mozilla are removing RSS feed discovery and display features from Firefox in an upcoming release. This is an unfortunate decision which will actively harm the open web, and should be reversed. It is also part of a larger pattern of unfortunate decisions by browser makers which contribute to a user-hostile network.
p1k3.com4slam, Tyng-Ruey Chuang, clacke@libranet.de ❌, Stephen Michael Kellat likes this.
4slam, clacke@libranet.de ❌, clacke@libranet.de ❌, clacke@libranet.de ❌ and 3 others shared this.
 I'm sad that RSS discovery was removed from prominence many years ago, but I totally buy their reasoning around Live Bookmarks. They never worked all that well, and the functionality should be put into an external competent RSS Reader instead -- like e.g. Mozilla's own Thunderbird.
I'm sad that RSS discovery was removed from prominence many years ago, but I totally buy their reasoning around Live Bookmarks. They never worked all that well, and the functionality should be put into an external competent RSS Reader instead -- like e.g. Mozilla's own Thunderbird.
That is indeed a sad development :-( I will add a visible RSS link to my own web site/blog so that people can still find the RSS feed.
2018-07-24T07:14:46Z via social.gl-como.it To: Public
How to stop Firefox from making automatic connections | Firefox Help
Learn about the various reasons why Firefox makes automatic connections to the Internet and how you can stop it from doing so if you wish.
support.mozilla.org2018-07-23T20:33:01Z via social.gl-como.it To: Public
Privacy Tools | Encryption against global mass surveillance
You are being watched! Knowledge, encryption and privacy tools to protect you against global mass surveillance.
www.privacytools.ioStephen Michael Kellat likes this.
Stephen Michael Kellat shared this.