
Igorette igorette@identi.ca

Evan Prodromou at 2022-10-28T03:42:52Z
Wow, I haven't used this service in a long timeJohn Patterson, Igorette, Thomas Jollans, Dan Scott and 5 others likes this.
Wikimedia Italia, ostfriesenmärz shared this.
Show all 6 replies
The Cat Model of Package Ownership
Elena ``of Valhalla'' at 2016-08-03T18:03:08Z
Debian has been moving away from strong ownership of packages by package maintainers and towards encouraging group maintainership, for very good reasons: single maintainers have a bad bus factor and a number of other disadvantages.
When single maintainership is changed into maintainership by a small¹, open group of people who can easily communicate and sync with each other, everything is just better: there is an easy way to gradually replace people who want to leave, but there is also no duplication of efforts (because communication is easy), there are means to always have somebody available for emergency work and generally package quality can only gain from it.
Unfortunately, having such group of maintainers for every package would require more people than are available and willing to work on it, and while I think it's worth doing efforts to have big and important packages managed that way, it may not be so for the myriad of small ones that make up the long tail of a distribution.
Many of those packages may end up being maintained in a big team such as the language-based ones, which is probably better than remaining with a single maintainer, but can lead to some problems.
My experience with the old OpenEmbedded, back when it was still using monotone instead of git² and everybody was maintaining everything, however, leads me to think that this model has a big danger of turning into nobody maintains anything, because when something needs to be done everybody is thinking that somebody else will do it.
As a way to prevent that, I have been thinking in the general direction of a Cat Model of Package Ownership, which may or may not be a way to prevent some risks of both personal maintainership and big teams.
The basic idea is that the “my” in “my packages” is not the “my” in “my toys”, but the “my” in “my Cat, to whom I am a servant”.
As in the case of a cat, if my package needs a visit to the vet, it's my duty to do so. Other people may point me to the need of such a visit, e.g. by telling me that they have seen the cat leaving unhealty stools, that there is a bug in the package, or even that upstream released a new version a week ago, did you notice?, but the actual putting the package in a cat carrier and bringing it to the vet falls on me.
Whether you're allowed to play with or pet the cat is her decision, not mine, and giving her food or doing changes to the package is usually fine, but please ask first: a few cats have medical issues that require a special diet.
And like cats, sometimes the cat may decide that I'm not doing a good enough job of serving her, and move away to another maintainer; just remember that there is a difference between a lost cat who wants to go back to her old home and a cat that is looking for a new one. When in doubt, packages usually wear a collar with contact informations, trying to ping those is probably a good idea.
This is mostly a summer afternoon idea and will probably require some refinement, but I think that the basic idea can have some value. Comments are appreciated on the federated social networks where this post is being published, via email (valid addresses are on my website and on my GPG key) or with a post on a blog that appears on planet debian.
¹ how small is small depends a lot on the size of the package, the amount of work it requires, how easy it is to parallelize it and how good are the people involved at communicating, so it would be quite hard to put a precise number here.
² I've moved away from it because the boards I was using could run plain Debian, but I've heard that after the move to git there have been a number of workflow changes (of which I've seen the start) and everything now works much better.Igorette, Tyng-Ruey Chuang, Daniel Koć, sazius and 4 others likes this.
Claes Wallin (韋嘉誠), Claes Wallin (韋嘉誠), der.hans, Christine Lemmer-Webber shared this.

@Laura Arjona well, they can't actually run away, but people can notice them and identify them as probably in need of a new hooman (at least if they have been actually abandoned).

Ben Sturmfels at 2015-03-23T14:33:06Z
At LibrePlanet, Seth Shoen demonstrated Let's Encrypt to obtain and install a new TLS certificate with a single command in only a matter of seconds. Will be awesome when it's live.
Igorette, Kevin Ford, Christine Lemmer-Webber, jrobb and 2 others likes this.
Claes Wallin (韋嘉誠), Claes Wallin (韋嘉誠) shared this.

Not yet, but keep an eye on http://media.libreplanet.org/. It's MediaGoblin, so you can subscribe to the news feed.


Why a free automated certificate authority is not the solution
The answer is simple: It's a certificate authority.
The certificate authority system is inherently flawed, this was not only proven by the fact governments as well as criminals could take over broadly accepted certificate authorities in the past, or that these takeovers had to be patched by software updates of a myriad of browsers, operating systems and other software.
It is flawed because it has that huge attack vector, there are over over 50 organizations that are trusted by your browser and they gave out the privilege to issue certificates for any domain to hundreds of other organizations. Remember this model is about trust. Do you trust all these or even the 50 root CAs? Did you verify they properly handle the power they've obtained? I did not, it's too much work.
Adding just yet another organization that can issue certificates for any domain only strengthens that model. It ensures future revenues for the companies providing you the nice little green icons in your browser, called "extended validation". I will leave looking up the prices for such a EV certificate and the estimate of how much real man work goes into that as an exercise for the reader.
There's hope though. For a few years now there's a new standard in the making, called "DNS-based Authentication of Named Entities", DANE for short. It's based on DNSSEC, an effort to prevent forged and not authoritative answers in the DNS system. In short DNSSEC guarantee's that the IP you're connecting to is controlled by the owner of the domain and DANE guarantees that there's no middle-man in your connection to the webserver listening on that IP.
DNSSEC reduces the number of entities you have to trust to effectively one, IANA. IANA does contract third parties to operate the root zone, currently this is VeriSign. Every signature can be chased to that single trusted party. To forge a domain you would need to compromise the root zones key, which is guarded by high standards, much higher than the ones of your average certificate authority. Also if you compromise at that level, you need to mirror the infrastructure of the whole top level domain your target domain is part of. This is feasible but also visible to monitoring systems. Attacking a top level domain infrastructure directly is also possible, the effect is greatly reduced though, only that single top level domain is compromised. You can't change the keys here either, as you would need to update the signatures in the root zone. And again an attack is more visible here.
Whether this is really greatly reducing the attack vector is debatable, what it objectively reduces is the damage you can make. Remember to compromise the current system on a whole you just need one of the hundreds of little certificate authorities.
You can activate DANE validation today through an excellent browser extension provided by the Czech domain registry. After you have installed it you can see that all my sites already deploy it, it's certainly possible.
I can understand if companies that benefit from the current system embark in such a "free" registry. I can understand if the EFF supports such a system as a short term measure, they don't directly influence any of the major software systems that would need to be adapted.
What makes me angry is that Mozilla is spending a lot of money to support it, while completely neglecting DANE support. There's no real progress for years now. They support the old broken system while they really could change something. If a major browser vendor like Mozilla shipped DANE support, across all its products, it would boost adoption of it a lot.
#mozilla #ssl #dns #dnssec #dane #letsencrypt
Igorette, lainfinity, jrobb, lnxwalt@microca.st and 9 others likes this.
Igorette, Olivier Mehani, Freemor, Douglas Perkins and 2 others shared this.
Show all 8 replies There is a pretty good summary of the issues (including with DANE) and existing (or not) solutions to the SSL CA problem in the October issue of the Communications of the ACM (nice video for layish people there): Security Collapse in the HTTPS Market. An insightful read.
There is a pretty good summary of the issues (including with DANE) and existing (or not) solutions to the SSL CA problem in the October issue of the Communications of the ACM (nice video for layish people there): Security Collapse in the HTTPS Market. An insightful read.
DANE did sound like the best solution to me, particularly for machine-to-machine verification (e.g., Pumps with self-signed certs didn't really federate last I tried), but the article points out that it is not all good. I'm glad that Jonne Hass wrote this. Some of these same ideas have been swirling in my head all day. That said, DNS (even with DNSSEC) is laughably insecure and (because it is centralized) the weakest point in the entire Internet.
I'm glad that Jonne Hass wrote this. Some of these same ideas have been swirling in my head all day. That said, DNS (even with DNSSEC) is laughably insecure and (because it is centralized) the weakest point in the entire Internet.lnxwalt@microca.st at 2014-11-19T03:49:33Z
jpope, Claes Wallin (韋嘉誠) likes this.

Evan Prodromou at 2014-11-03T21:23:45Z
I think there's a lot of value for an OStatus bridge for pump.io.ostfriesenmärz, Claes Wallin (韋嘉誠), Igorette, Scott Sweeny and 4 others likes this.

Calling all our wonderful podmins!
It appears that someone has been spreading false information to podmins around the network, suggesting that podmins of smaller pods close down their pod because of some current issues with federation. This is rubbish, and these statements are not endorsed by any "official authority".
It's true that diaspora* has some issues with distributing content effectively throughout the network. Some comments or likes may not appear on all pods, and occasionally an image may appear twice. But there are people working to solve these issues.
Closing small pods wouldn't help these issues at all. diaspora* is a decentralized network which will only keep growing and stay healthy if the number of smaller nodes in the network keeps increasing, as it has been. That's why the software is open and available for anyone to install and run. Small pods are not a problem at all; in fact, the network needs small pods to keep improving. It's some of the very large pods which tend to have some problems with federation, because of the high traffic flowing in and out of them. diaspora* wasn't designed to accommodate such huge pods, and so podmins of some of our largest pods face some difficulties to keep performance at an optimum level.
To keep growing and becoming healthier, diaspora* needs more small pods, not fewer. The ideal that we'd like to work towards is where diaspora*'s membership is widely and more evenly distributed around a huge number of smaller pods.
If you are thinking of setting up a pod, either just for yourself and friends or as an open pod, don't be put off by anything you might have read recently saying that small pods are a problem. They are part of the solution!
And if you are running a pod of any size, large or small, you are one of the people who is keeping this network alive! Don't listen to anyone who tries to tell you any different. You are part of the beating heart which makes diaspora* awesome! We love you!
#diaspora #podmin #podmins #announcement
via Diaspora HQ - LinkDigital Roffey, Aqeel Zafar, habi@fmrl.me, jrobb and 9 others likes this.
Claes Wallin (韋嘉誠), Claes Wallin (韋嘉誠), Claes Wallin (韋嘉誠), Stephen Michael Kellat and 2 others shared this.
 Version 0.4.0 available for Linux & Windows: http://terminal-overload.org #tol #free #opensource #floss #indie #fps #game #linuxgaming #torque3d
Version 0.4.0 available for Linux & Windows: http://terminal-overload.org #tol #free #opensource #floss #indie #fps #game #linuxgaming #torque3d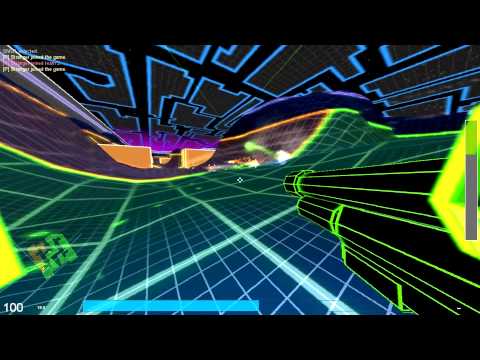
Terminal OverloadLatest news: Oct. 12 2014: Version 0.3.1 is available for Linux and Windows. What's new?
joemaro, Juegos GNU/Linux, Igorette, Christine Lemmer-Webber likes this.
Juegos GNU/Linux, Juegos GNU/Linux, Juegos GNU/Linux, Dana and 3 others shared this.
 Just learned about a massive git-annex deployment, spanning multiple organizations, 100 terabytes of data, and with complications including mailing hard drives, Debian VMs on Windows, and custom GUI interfaces. Hoping I can share some details sometime, it's awesome!
Just learned about a massive git-annex deployment, spanning multiple organizations, 100 terabytes of data, and with complications including mailing hard drives, Debian VMs on Windows, and custom GUI interfaces. Hoping I can share some details sometime, it's awesome!
The really great thing about it is that when they're older, my great-neice and nephew will quite likely at some point use some of this data. This is all about preserving an important part of their cultural heritage.Arthur Lutz, Igorette, Nicola Busanello, Aeva Ntsc and 13 others likes this.
Christine Lemmer-Webber, Claes Wallin (韋嘉誠), Stefano Zacchiroli shared this.

Ah, I suppose this is one of the institutional sponsors and that this is what you can disclose at the moment. Very cool to hear, thanks for sharing.
 Also: you have a great-niece and a great-nephew?
Also: you have a great-niece and a great-nephew?Evan Prodromou at 2013-11-14T16:21:14Z
Greg Grossmeier likes this.

Sarven Capadisli at 2013-08-13T16:44:39Z
Black Mirror: http://www.imdb.com/title/tt2085059
6 episodes. Watch it!
#Technology #HCI #SciFi #AugmentedReality
ostfriesenmärz at 2013-08-06T09:26:34Z
"everything is a stream" -> http://blog.rivva.de/everything_is_a_stream #rivvaIgorette likes this.

Impeller 0.6.0 - The Tablet Edition

The rich client for Pump.io
 or other options via the website
or other options via the websiteBug
- [IMP-88] - Cannot post full-res photos
- [IMP-92]
- java.lang.IllegalArgumentException: Activity PostActivity does not
have a parent activity name specified.
Improvement
- [IMP-93] - Better image loading performance
New Feature
- [IMP-91] - Tablet UI
Maj, Igorette, jcsesecuneta@fmrl.me, Moparx and 4 others likes this.
Moparx, Evan Prodromou shared this.
Show all 7 replies
Matthias Kirschner at 2013-07-24T06:54:12Z
Wo auf jeden Fall niemand auf die Argumente eingeht: Update zu meiner Kommunikation mit der #Rundfunkgebührenanstalt https://blogs.fsfe.org/mk/?p=1025Igorette likes this.

Christine Lemmer-Webber at 2013-07-22T21:41:00Z
Oh wow cool! First "in the wild" use of PyPump? PumpMigrate... migrate between instances!
https://gitorious.org/pumpmigrate
How long did it take for migration tools to appear for StatusNet? It's awesome to have them so soon for pump.io!Mark Holmquist, ostfriesenmärz, Igorette, David Nelson and 10 others likes this.
ostfriesenmärz, Jonas (kabniel), Star, Sander shared this.

ostfriesenmärz at 2013-07-15T07:42:35Z
langsam könnte sich meine alte timeline mal wieder blicken lassen.Igorette likes this.
Jarilo shared this.
 Für mich macht das hier keinen Sinn. Komme mit Ipad hier nicht rein, finde auch keine pasende App. Außerdem vermisse ich hier die Möglichkeit, sich zu unterhalten
Für mich macht das hier keinen Sinn. Komme mit Ipad hier nicht rein, finde auch keine pasende App. Außerdem vermisse ich hier die Möglichkeit, sich zu unterhalten @wako *wink* es gibt leider noch keine ios-app, aber auf meinem ipad funktionierts größtenteils. gelegentlich hilfts die seite neu zu laden ... ;) und unterhalten geht doch auch schon?
@wako *wink* es gibt leider noch keine ios-app, aber auf meinem ipad funktionierts größtenteils. gelegentlich hilfts die seite neu zu laden ... ;) und unterhalten geht doch auch schon? das mit dem Ipad ist komisch. Mit neuladen hat das nicht zu tun, meine Anmeldung bleibt hängen :( Unterhalten, nein, dann man kann immer wieder nur ein Comment an deine erste Nachricht senden und @wako funzst nicht würde schnell untergehen, bekomme keine Email und der thread kommt auch nicht nach "oben"
das mit dem Ipad ist komisch. Mit neuladen hat das nicht zu tun, meine Anmeldung bleibt hängen :( Unterhalten, nein, dann man kann immer wieder nur ein Comment an deine erste Nachricht senden und @wako funzst nicht würde schnell untergehen, bekomme keine Email und der thread kommt auch nicht nach "oben" mit den kommentaren hast Du natürlich recht. einigen wir uns auf 'eingeschränkt möglich'? ;) für die ganzen sachen gibt es aber schon bugreports, so dass das höchstwahrscheinlich bald kommen wird. ipad hängen klingt komisch. bei mir hilft dann manchmal ein tippen aufs 'identi.ca' oben links. [oder eben die seite noch mal neu zu laden.]
mit den kommentaren hast Du natürlich recht. einigen wir uns auf 'eingeschränkt möglich'? ;) für die ganzen sachen gibt es aber schon bugreports, so dass das höchstwahrscheinlich bald kommen wird. ipad hängen klingt komisch. bei mir hilft dann manchmal ein tippen aufs 'identi.ca' oben links. [oder eben die seite noch mal neu zu laden.]
Evan Prodromou at 2013-07-11T11:44:35Z
There seems to be a problem with the password recovery on identi.ca. I'm trying to trace it down; I think it might have to do with firewalls and the remote mail server.
Thanks for being patient, folks.
Luckily, my flight is delayed, so I have some time to look into this.ZettaGeek, herath72, Greg Grossmeier, Igorette and 5 others likes this.
RC, Richard Fontana, netgeek, morgenland and 2 others shared this.
Show all 12 replies Pump.io looks great. Thanks for all the work that went into it. Is it possible to embed my public feed on my website, like it was with status.net? More generally, where's the right place to ask Pump.io questions?
Pump.io looks great. Thanks for all the work that went into it. Is it possible to embed my public feed on my website, like it was with status.net? More generally, where's the right place to ask Pump.io questions?Steven Murdoch at 2013-07-11T20:53:50Z
Evan Prodromou likes this.
 Errr. Choqok doesn't work. What can I do to make it functional again ? Or it is incompatible with the new Identi.ca ?
Errr. Choqok doesn't work. What can I do to make it functional again ? Or it is incompatible with the new Identi.ca ?
Deceased. Please use 'andyc@pumpdog.me'. at 2013-06-13T19:10:07+00:00
Pump Issue #1: 'The Social Web is not federated' - http://ur1.ca/eb86mHilton Garcia Fernandes, X11R5, alek, Stefano Costa and 3 others likes this.
Steven Rosenberg, Blaise Alleyne, axel668 (inactive), Hilton Garcia Fernandes and 3 others shared this.
 @andyc: reminds me of something, but I really can't say what exactly… ;)
@andyc: reminds me of something, but I really can't say what exactly… ;)Stefano Zacchiroli at 2013-06-14T12:03:00+00:00
Christine Lemmer-Webber likes this.

plomlompom at 2013-04-16T10:06:49+00:00
Twitter sperrt Flattr. Begründung: Die Favs unserer User gehören nur uns. http://ur1.ca/deix0 Merkt euch das, wenn ihr favt.Igorette likes this.

Rob Connolly at 2010-09-23T23:10:44+00:00
The wikipedia list looks even better: http://en.wikipedia.org/wiki/List_of_Open_Source_Android_Applications !android !replicantIgorette likes this.

DokuWiki at 2010-10-07T08:25:30+00:00
The new release candidate "Lazy Sunday is out: http://ping.fm/kqCzu /alIgorette likes this.