
Kevin Everets keverets@identi.ca
Canada
Interests in Free Software, sustainability, music, motorcycling, bicycling, and making the world better bit by bit
2016-11-04T09:56:57Z via AndStatus To: Public
@freemore@identi.ca looks like Ring is now a GNU project. Have you tried it again recently? Curious if it's actually usable yet.
Christine Lemmer-Webber shared by Kevin Everets at 2016-09-14T00:00:14Z via AndStatus To: Public
@Alex Jordan I used el-get and the package system for a long time, but there are a few reasons why I prefer to use Guix. For one thing, I'm not sure what the security situation of ELPA is; are there checksums, etc? I don't know. I know what Guix's situation is.
I've also had upgrades with emacs packages where I really wished I hadn't upgraded, and that I could roll back so I could fix up my emacs config for the new version at my leisure. That comes for free with Guix.
Claes Wallin (韋嘉誠), AJ Jordan likes this.
Kevin Everets shared this.
Evan Prodromou shared by Kevin Everets at 2016-09-06T17:35:03Z via AndStatus To: Public
'm very proud to say that the W3C working group I've been involved with for the last couple of years has published a Candidate Recommendation for Activity Streams 2.0.Activity Streams is a JSON format for encoding information about activities on a social network. Who posted a status update? When? Who liked it? Who commented on it, and what did they say?The format allows social networking software to interoperate -- exchanging information about people and stuff on the networks in a standard way. That helps with doing things like backing up your social network information, or sending live updates between networks.Programmers should start implementing Activity Streams in their software ASAP. Non-programmers should start asking for Activity Streams support in the software and services they use.Thanks a ton to friends and colleagues on the W3C Social Working Group for getting us to this point.Christophe Schockaert, Sean Tilley, Malvin, Blaise Alleyne and 22 others likes this.
Christophe Schockaert, Screwtape, mnd, mnd and 12 others shared this.
Show all 7 replies @mray@identi.ca No. That's in the future.
@mray@identi.ca No. That's in the future.Claes Wallin (韋嘉誠) at 2016-09-07T05:10:01Z
AJ Jordan likes this.
 https://www.w3.org/TR/activitystreams-vocab/ -- 404. Link taken from https://www.w3.org/Social/WG page
https://www.w3.org/TR/activitystreams-vocab/ -- 404. Link taken from https://www.w3.org/Social/WG page
Fixed, thank you @mnd, it now points to https://www.w3.org/TR/activitystreams-vocabulary/
Elena ``of Valhalla'' shared by Kevin Everets at 2016-08-31T20:35:38Z via AndStatus To: Public

Facebook Recommended That This Psychiatrist's Patients Friend Each OtherAnd she has no idea why it's happening.
Bd Sn, jrobertson likes this.
EricxDu, EricxDu, Bd Sn, der.hans and 1 others shared this.
 This is a terrific example of the unintended consequences (from the end users' points of view) of sharing contact information (and so much more) with these entities. I try not to beat people over the head on these issues, but I've definitely been sharing this story with loved ones to try to raise awareness of the fact that while they think "they have nothing to hide" that they actually do, and we need to protect each other from corporate surveillance.
This is a terrific example of the unintended consequences (from the end users' points of view) of sharing contact information (and so much more) with these entities. I try not to beat people over the head on these issues, but I've definitely been sharing this story with loved ones to try to raise awareness of the fact that while they think "they have nothing to hide" that they actually do, and we need to protect each other from corporate surveillance.Charles Stanhope at 2016-08-31T15:51:56Z
der.hans, Christine Lemmer-Webber, Elena ``of Valhalla'' likes this.
Free Software Foundation shared by Kevin Everets at 2016-08-16T21:12:46Z via AndStatus To: Public
#DRM-encumbered version of Firefox now available on GNU/Linux. We won't be installing it. Adding DRM to any version was a mistake, as we said when Mozilla announced this in 2014: https://u.fsf.org/z0wilo, Francisco M García Claramonte, Christine Lemmer-Webber, B. Ross Ashley and 2 others likes this.
wilo, wilo, jrobertson, jrobertson and 8 others shared this.
Christine Lemmer-Webber shared by Kevin Everets at 2016-08-11T21:14:31Z via AndStatus To: Public
FSF asks for support of the LibreTea E0MA68 computer card
I've backed it!
der.hans, Charles Stanhope likes this.
der.hans, Kevin Everets shared this.
 how could I, if I can only view the crowdfunding site through the web archive, because of its use of cloudflare and the proprietary captcha software it uses to stop me from contributing? :-(
how could I, if I can only view the crowdfunding site through the web archive, because of its use of cloudflare and the proprietary captcha software it uses to stop me from contributing? :-(Alexandre Oliva at 2016-08-14T08:21:40Z
lnxwalt@microca.st likes this.

I agree with @Alexandre Oliva For a project applying for aRYF this should be an issue that is getting discussed before RYF certification is granted. Cloudflare definitely does not RYF. People using Cloudflare arn't RYF'ing
Freemor at 2016-08-14T12:46:58Z
lnxwalt@microca.st likes this.
Free Software Foundation shared by Kevin Everets at 2016-08-11T12:05:13Z via AndStatus To: Public
Support the Libre Tea Computer Card, a candidate for Respects Your Freedom certification. #RYF https://u.fsf.org/1vkRiveraValdez, kesara, Jason Self likes this.
RiveraValdez, Kevin Everets, Kevin Everets, Kevin Everets and 3 others shared this.
Free Software Foundation shared by Kevin Everets at 2016-08-11T12:05:12Z via AndStatus To: Public
Support the Libre Tea Computer Card, a candidate for Respects Your Freedom certification. #RYF https://u.fsf.org/1vkRiveraValdez, kesara, Jason Self likes this.
RiveraValdez, Kevin Everets, Kevin Everets, Kevin Everets and 3 others shared this.
Free Software Foundation shared by Kevin Everets at 2016-08-11T12:05:11Z via AndStatus To: Public
Support the Libre Tea Computer Card, a candidate for Respects Your Freedom certification. #RYF https://u.fsf.org/1vkRiveraValdez, kesara, Jason Self likes this.
RiveraValdez, Kevin Everets, Kevin Everets, Kevin Everets and 3 others shared this.
Renato Candido shared by Kevin Everets at 2016-08-10T17:21:51Z via AndStatus To: Public
The #sharing economy is bullsh!t. Here’s how we can take it back http://grist.org/politics/the-sharing-economy-is-bullsht-heres-how-we-can-take-it-back/der.hans, B. Ross Ashley, Freemor likes this.
Kevin Everets, Freemor shared this.
Bits from Debian: Debian and Tor Services available as Onion Services
Debian Project shared by Kevin Everets at 2016-08-02T16:24:15Z via AndStatus To: Public
Link to original post: Debian and Tor Services available as Onion ServicesWe, the Debian project and the Tor project are enabling Tor onion services for several of our sites. These sites can now be reached without leaving the Tor network, providing a new option for securely connecting to resources provided by Debian and Tor.
The freedom to use open source software may be compromised when access to that software is monitored, logged, limited, prevented, or prohibited. As a community, we acknowledge that users should not feel that their every action is trackable or observable by others. Consequently, we are pleased to announce that we have started making several of the various web services provided by both Debian and Tor available via onion services.
While onion services can be used to conceal the network location of the machine providing the service, this is not the goal here. Instead, we employ onion services because they provide end-to-end integrity and confidentiality, and they authenticate the onion service end point.
For instance, when users connect to the onion service running at http://sejnfjrq6szgca7v.onion/, using a Tor-enabled browser such as the TorBrowser, they can be certain that their connection to the Debian website cannot be read or modified by third parties, and that the website that they are visiting is indeed the Debian website. In a sense, this is similar to what using HTTPS provides. However, crucially, onion services do not rely on third-party certification authorities (CAs). Instead, the onion service name cryptographically authenticates its cryptographic key.
In addition to the Tor and Debian websites, the Debian FTP and the Debian Security archives are available from .onion addresses, enabling Debian users to update their systems using only Tor connections. With the apt-transport-tor package installed, the following entries can replace the normal debian mirror entries in the apt configuration file (
/etc/apt/sources.list):deb tor+http://vwakviie2ienjx6t.onion/debian jessie main deb tor+http://vwakviie2ienjx6t.onion/debian jessie-updates main deb tor+http://sgvtcaew4bxjd7ln.onion/debian-security jessie/updates main
Likewise, Tor's Debian package repository is available from an onion service :
deb tor+http://sdscoq7snqtznauu.onion/torproject.org jessie main
Where appropriate, we provide services redundantly from several backend machines using OnionBalance. The Debian OnionBalance package is available from the Debian backports repository.
Lists of several other new onion services offered by Debian and Tor are available from https://onion.debian.org and https://onion.torproject.org respectively. We expect to expand these lists in the near future to cover even more of Debian's and Tor's services.
Jakukyo Friel, Marcelo Santana, kenyahhtah, guile and 8 others likes this.
Jakukyo Friel, Marcelo Santana, Claes Wallin (韋嘉誠), Kevin Everets and 10 others shared this.
Schneier on the security of our election systems
Christine Lemmer-Webber shared by Kevin Everets at 2016-07-30T14:31:08Z via AndStatus To: Public
AJ Jordan, Charles Stanhope likes this.
AJ Jordan, Stephen Michael Kellat, Kevin Everets shared this.
Show all 5 replies
I'm going to quibble on one point. Securing the back-end is one thing. As to the front-end, we disarm ourselves pretty easily by not registering voters properly or striking down voter ID laws. If we have no way to authenticate who presents themselves to vote at a single precinct, making sure things are fine on the back-end kinda doesn't matter. As a former precinct elections official, these quite insane judicial rulings over the past few days striking down photo ID have been hilarious as they tear down any hope of security on the front-end in terms of ensuring that one qualified and eligible person gets one vote in the correct precinct. As to the inability to gain photo ID due to the lack of required underlying documents being touted as the reason for voiding these laws...how are these people surviving in a society that requires positive photo ID for an awfully large number of transactions beyond just voting these days?
 Not having ID is normal enough. I'm an American citizen and I live in Japan. When I visit the U.S., the only U.S.-issued ID I have is my passport. But my passport should be for entering and leaving the country, not for anything else. Also, it's just one document which I could lose, if I were careless or unlucky. And the more I carry it around, the more I risk losing it, which would be a total disaster. If I want to renew my long-since expired drivers license, I either need to go back to North Dakota (which is far, so I don't often go there) or somehow prove that I live in a place where I'm just visiting. We're not legally required to have or carry photo ID in the U.S. Just because lots of places would prefer we did doesn't change that fact.
Not having ID is normal enough. I'm an American citizen and I live in Japan. When I visit the U.S., the only U.S.-issued ID I have is my passport. But my passport should be for entering and leaving the country, not for anything else. Also, it's just one document which I could lose, if I were careless or unlucky. And the more I carry it around, the more I risk losing it, which would be a total disaster. If I want to renew my long-since expired drivers license, I either need to go back to North Dakota (which is far, so I don't often go there) or somehow prove that I live in a place where I'm just visiting. We're not legally required to have or carry photo ID in the U.S. Just because lots of places would prefer we did doesn't change that fact.
Just for lulz I try presenting my Japanese ID whenever visiting the U.S. and people ask. One time I went to a karaoke bar in NYC, and the bartender was Japanese-American who had lived in the U.S. for a long long time, and he didn't know the Japanese year scheme (it's currently the Heisei era), so he couldn't figure out if I was 21 or not.Douglas Perkins at 2016-07-31T01:24:18Z
Claes Wallin (韋嘉誠), jasonriedy@fmrl.me likes this.
 > We're not legally required to have or carry photo ID in the U.S.
> We're not legally required to have or carry photo ID in the U.S.
I don't know whether he was just blowing smoke, but I did have a discussion with an off-duty cop who told me that California does in fact require one to carry currently-valid government-issued photo ID at all times.
My actual beef was and is the expiration date. Do I stop being myself if some identification document expires?
@lnxwalt@microca.st I think you have been misled. AFAIK there are no generic legal requirements to possess or carry a photo ID in the U.S. in any state. (Practically speaking it would make many things difficult if you didn't have one at all, but that's a separate issue.)
In California, I know some cities require you carry ID if you're driving a car or (more notably) riding a bicycle on a public road. If there were a generic "must-carry-ID" state statute, the city statute would probably not exist, because it would be pointless.
Douglas Perkins at 2016-07-31T07:06:40Z
Sarah Elkins likes this.
Meanwhile in a climate summit...
shared by Kevin Everets at 2016-07-18T19:52:52Z via AndStatus To: Public
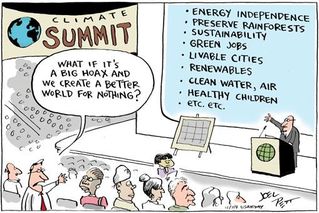
Claes Wallin (韋嘉誠), --, Marcos, EVAnaRkISTO and 2 others likes this.
der.hans, EVAnaRkISTO, ghostdancer, Doug Whitfield and 5 others shared this.

DON'T YOU DARE DO ALL THOSE GOOD THINGS FOR NO REASON!!
JanKusanagi at 2016-07-18T20:14:13Z
EVAnaRkISTO, Douglas Perkins likes this.
How do we know...?: the age of the universe
Stephen Sekula shared by Kevin Everets at 2016-07-17T20:44:36Z via AndStatus To: Public

How do physicists know the age of the universe? Independent data samples taken over decades all tell a consistent story when the known laws of physics are applied: the way that distant objects all recede from our vantage point, the properties of the low-energy microwaves that arrive at Earth from all different directions, the relative abundance of light atomic elements in the observable cosmos, and many others all tell the same story: the universe is 13.799 billion years old, and because we're responsible scientists who quantify the limits of our knowledge, we assign an uncertainty to that number based on the way we interpret the data and the physical constraints on our measurements: a measly 0.021 billion years (just a 1.5% uncertainty).
This age is arrived at by assuming a universe of space and time containing radiation (e.g. light), two kinds of matter ("baryonic" - the stuff you and me and Earth and stars are made from - and "dark" - the unseen matter that shapes the large scale structure of the cosmos), and an inherent energy density in the cosmos. If any of those assumptions were wrong, then modern medicine, chemistry, and engineering would have been impossible and would have never happened. The fact that you can have an MRI or PET scan, or that you can create new life-saving drugs to kill the nastiest cancers, or that the GPS satellite system could be engineered at all, is entirely tied to the same laws that underpin our understanding of the age of the universe. There is no modern world without an ancient cosmos.
Alternative scientific explanations for the observations of the cosmos exist, but have failed to explain or predict all observations, making them weak and discreditied ideas. Non-scientific explanations for the cosmos, including purely philosophical or religious explanations, have all also failed to predict all of these observations before they were made and are often unfalsifiable or even completely untestable, making them unscientific, outside the natural world, and thus useless for making independent and reliable judgements about the content of the universe.
Image by the NASA/WMAP Science Team - Original version: NASA (http://map.gsfc.nasa.gov/media/060915/index.html ); modified by Ryan Kaldari.
Learn more about the observations that yield our modern, reliable, and reproducible understanding of the age of the universe from these sources:
http://www.symmetrymagazine.org/article/august-2015/the-age-of-the-universe
http://www.symmetrymagazine.org/article/what-could-dark-matter-be
http://www.symmetrymagazine.org/article/february-2012/cosmic-microwave-background
John Hume likes this.
Kevin Everets shared this.
Free Software Foundation shared by Kevin Everets at 2016-07-11T21:17:03Z via AndStatus To: Public
Free/Libre alternatives to GAFAM's Internet: a review of French initiatives
LibrePlanet video available: https://media.libreplanet.org/u/libreplanet/collection/free-libre-alternatives-to-gafam-s-internet-a...Marianne Corvellec, April and Jonathan Le Lous, April
Project "De-google-ify Internet" aims at offering as many alternative services as possible to those threatening our digital freedoms. Google is not the only player there, even though it gave the project its name. Google Drive, Google Calendar, Skype, Dropbox, Facebook, Twitter, Youtube, Doodle, Yahoo Groups, and many others, are extremely convenient services. But they are centralized and make users dependent.
Framasoft are resisting this trend. They have come up with a several year roadmap to set up alternative services. These services are thought of as digital commons. They are free, gratis, and open to all. Framasoft is a French not-for-profit whose goal is to decentralize the Internet by promoting self-hosting. They work to empower everyone to install and run their own services. The project already offers more than 15 alternative services and welcomes about 1,000,000 visits per month.
bthall, Krugor, sazius, Douglas Perkins and 1 others likes this.
Krugor, Stephen Michael Kellat, Kevin Everets, A Bitter Ray of Sleet and 1 others shared this.
2016-07-01T18:55:36Z via Identi.ca Web To: Public CC: Followers
I was trying to load an OpenStreetMap based map into a Garmin Zumo 220 (motorcycle optimized GPS), and I was running into problems. I could generate the map for the appropriate region from http://garmin.openstreetmap.nl/ but when placing the final gmapsupp.img file into the "Garmin/" directory on the device, the system software would never find it. It was not visible under Tools -> Settings -> Map -> Map Info. Only the original base map showed up.
I tried replacing the ".System/gmapprom.img" with the gmapsupp.img and found that the map was then picked up (but incomplete since I hadn't selected the entire continent due to space constraints on the GPS). So, the file seemed good, but why could I not augment the existing map?
I finally found the answer in:
https://forums.garmin.com/archive/index.php/t-73886.html
There it was described about the "Garmin/GarminDevice.xml" file that defines where it expects to find files. Reading that file revealed that "gmapsupp.img" must be placed in the "Map/" directory, not in the "Garmin/" or ".System/" directories.
Sometimes even simple things can take a while.Douglas Perkins likes this.
Douglas Perkins, Douglas Perkins, Douglas Perkins shared this.
Green, libre, and eventually RYF?
Christine Lemmer-Webber shared by Kevin Everets at 2016-07-01T14:28:55Z via AndStatus To: Public
Huh. Crowdfunded Libre Hardware Design'ed laptop/computer. Apparently low power.
Offering refund if RYF certification doesn't happen, which is interesting!
der.hans, Tyng-Ruey Chuang, lnxwalt@microca.st, Douglas Perkins and 6 others likes this.
Jason Self, Kevin Everets, Charles Stanhope, mray INACTIVE shared this.
Watch Bradley in Copyleft for the next decade: a comprehensive plan
shared by Kevin Everets at 2016-06-24T21:24:00Z via AndStatus To: Public

Copyleft has faced serious challenges in the last five years. It's not over: many more threats are on the way. Not by coincidence these attacks on copyleft come when "open source" reaches new heights of success. For example, hordes of software developers are funded full time to churn out new free software, as long as it's not copylefted. Some such code is specifically designed to replace existing, widely used, copylefted programs.
Meanwhile, programs under copyleft licenses (most notably the kernel named Linux) face a decades long, ongoing myriad of license violations. Such violations include nefarious attempts by major companies to shirk their responsibilities under copyleft. The situation is undoubtedly bleak.
Those of us who care about software freedom need a plan. Copyleft once assured an equal playing field, but big companies work daily to tilt the playing field in their favor and against the interests of most developers, hobbyists, users, and enthusiasts.
Arcee, Douglas Perkins likes this.
jrobertson, jrobertson, jrobertson, Douglas Perkins and 8 others shared this.

I like how Bradley says whether something is true doesn’t really matter because if everyone believes it, they’re going to act accordingly.
PS—I also like his suggestion for professional programmers: negotiating copyright during an interview.
PPS—Here’s a union that I asked to help with copyright. I’m a member, and I welcome everyone to join.
2016-06-23T02:46:41Z via AndStatus To: Public
Ignore the Scare Tactics: The Real Future of Bell Investment in Fibre Networks http://feedproxy.google.com/~r/MichaelGeistsBlog/~3/Q8EFatwYAj0/Sam Black shared by Kevin Everets at 2016-06-23T02:36:04Z via AndStatus To: Public
Wow. Twitter blocks people using alternate URL shorteners (like ur1.ca) because it might be spam or "malicious activity". Amazing. /ssazius, B. Ross Ashley, Douglas Perkins likes this.
Iñaki Arenaza, jrobertson, jrobertson, jrobertson and 10 others shared this.
Show all 7 replies
Funny. And replacing users' links with a link to their own shortener, while making it look like it's still the original link, isn't "malicious"?
The nerve...
lnxwalt@microca.st likes this.

Now come on.. How are they supposed to track who clicks what if ya use your own shortener? I'm sure in their view using an independent shortener is 'malicious' to their metrics which in turn is malicious to their bottom line. And I won't even start on how you're blowing their whole SEO dreams.
Interesting that this news comes on the day I decided not to follow any twitter pointing links. Tired of it not working unless I turn on cookies and JS just to see some pointless 140 char thing. Got better ways to waste my life thank-you.
Freemor at 2016-06-22T23:16:17Z
lnxwalt@microca.st likes this.
 Don't use url-shorteners. Besides, url's don't count towards the 140 character limit on Twitter any more.
Don't use url-shorteners. Besides, url's don't count towards the 140 character limit on Twitter any more.Scott Sweeny likes this.